|
#
About |
SpiderPig is a project created for performing and visualizing data
flow analysis of a selected binary program. SpiderPig was created in
the purpose of providing a tool which would be able to help
vulnerability and security researchers with tracing and analyzing
any necessary data and it's further propagation. Such tasks are very
often crucial in the vulnerability discovering/identifying process
and typically require a lot of time consuming manual work. The initial concept is
pretty old, the first pseudo usable version was created initialy for
Immunity
Debugger Plugin Contest back in the 2007 just to be frozen few
days after. I have reactivated the project while having the last
months of holidays (arround September 2008) and I have decided to
write a little paper about it (which was finished arround November
2008). Since i switched for another
research at the moment the SpiderPig research is practically frozen
since the time paper was made. As you probably realize history of this project
is kinda a nutty. Anyway enjoy or erm not enjoy.
|
|
# Paper |
|
Little paper called "Dynamic Data Flow Analysis via Virtual Code
Integration (aka The SpiderPig case)"
was released. It describes the
methods, testimonials and some other information related to SpiderPig . You can download it below:
Paper: Dynamic Data Flow Analysis via Virtual Code
Integration
(aka The SpiderPig case) - PDF
|
|
# Sample video
presentation + data flow graph |
The
video presentation attached below tries to illustrate the way
SpiderPig works. The vulnerability presented in the video is an old
and completely useless MS05-002 (triggered by some old exploit from
houseofdabus /
Ivanm - as far as I remember). I have picked this bug because it seems to be fairly
easy one, however as you will see in the video even though it's an
easy vulnerability the video material is kinda twisted and sometimes
not easily understandable (at least for other persons then myself).
After some requests I tried to add some subtitles to the video but
it seems they have only made things worse. The idea of this demo is
to demonstrate how to locate the vulnerability with usage of
SpiderPig and a working exploit (of course it can be done without it
too). Ok well, some aditional notes you should consider while
watching:
- the data is
gathered on emulated machine (the VM disk is located on some other
computer and accessed through the LAN), the data is exported to
other machine via LAN also, this decreases the performance a
bit
- neither pigs nor
spiders were hurt in the making of this video
I recommend to view this video
without the fullscreen HD mode unless you really want to see something
:) If you want actually to see it, try the HD quality by
following the link (vimeo),
and using the fullscreen mode button.
The graph illustrating the captured data
flow for this vulnerability can be found here:
GRAPH FILE
|
|
# Last things |
Like always any comments, advice,
error corrections are always welcome. So if you feel you have
something to say feel free to
contact me.
|
|
# Bonus -
why so serious - EXPAND? |
Since I havent released any source codes or binary codes I would
like to give all the readers an awesome bonus, which can keep you
satisfacted for entire months. Ladies and gentleman I present you
the one and not the only SPIDERPIG PAPERCRAFT created by
Jerom. Just print it, cut it, glue it and enjoy it (here is a
hint for the younger readers: I havent tried this myself but it
seems quite possible you may eat it as well of course with parents
supervision). Here it comes (click
for the larger version): 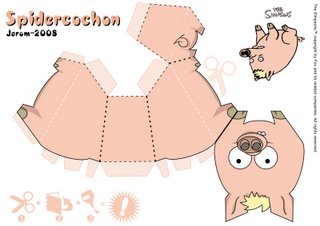
|